31 | Add to Reading ListSource URL: kvinderiledelse.dkLanguage: English - Date: 2014-10-22 04:44:54
|
|---|
32 | Add to Reading ListSource URL: shill.seas.harvard.eduLanguage: English - Date: 2015-01-27 03:23:54
|
|---|
33 | Add to Reading ListSource URL: www.la-samhna.deLanguage: English - Date: 2011-11-01 18:43:17
|
|---|
34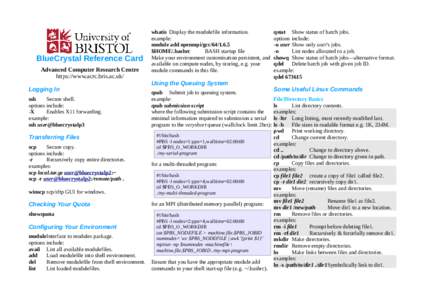 | Add to Reading ListSource URL: www.acrc.bris.ac.ukLanguage: English - Date: 2014-01-09 11:53:15
|
|---|
35 | Add to Reading ListSource URL: gotocon.comLanguage: English - Date: 2015-05-22 04:43:09
|
|---|
36 | Add to Reading ListSource URL: nsrc.orgLanguage: English - Date: 2014-08-06 02:22:19
|
|---|
37 | Add to Reading ListSource URL: conferences.sigcomm.orgLanguage: English - Date: 2009-07-22 15:07:11
|
|---|
38 | Add to Reading ListSource URL: www.nsa.govLanguage: English - Date: 2013-08-12 08:28:39
|
|---|
39 | Add to Reading ListSource URL: www.thestorkstopshere.comLanguage: English - Date: 2009-09-29 10:47:05
|
|---|
40 | Add to Reading ListSource URL: www.cs.kau.seLanguage: English - Date: 2014-05-26 09:37:41
|
|---|